
Phish-proofing your emails with Microsoft 365 Defender
Have you ever clicked on a link in an email that led you to a suspicious page asking for your information? You’re not alone. Phishing


Have you ever clicked on a link in an email that led you to a suspicious page asking for your information? You’re not alone. Phishing

Safeguarding your online privacy is becoming increasingly important as cyberthreats continue to rise. Private browsers offer a layer of protection by keeping your online activities

eCommerce thrives on happy customers, but managing a growing order volume can strain your ability to deliver exceptional experiences. What’s worse, traditional methods often fall

In the 1950s, hackers simply referred to individuals with curious minds tinkering with the potential of computers. However, the rise of personal computers in the

Are you searching for a communication solution that’s as dynamic as your business environment? Softphones emerge as a compelling contender, offering a host of features
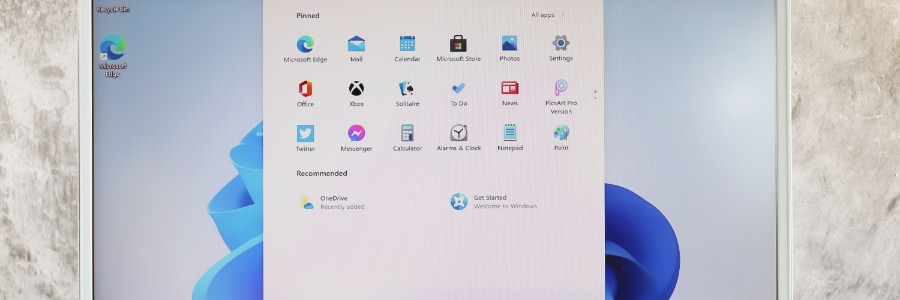
Windows comes with a plethora of default settings that aren’t to everyone’s taste and many users find extremely irritating. This guide helps you cut out

Website images are crucial for engaging visitors, conveying brand messaging, and showcasing products or services. Their impact on search engine optimization (SEO) has been often

The digital landscape is riddled with threats: malware attacks, phishing scams, and data breaches are just a few. But by taking a proactive approach to

Many businesses today can’t live without Voice over Internet Protocol (VoIP) systems, which provide a wealth of features and benefits, primarily cost savings and advanced

Wondering how your team can get past its productivity plateau? Feeling like there’s untapped potential hidden within your workflows? Your search for answers ends with
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Donec enim diam vulputate ut pharetra.